Automated Reward Wallet Attack Postmortem
What Happened, Our Response, & Path Forward
TLDR
On May 7, 2026, Moats App discovered unauthorized transfers from the automated reward wallets system stemming from a compromised backend administrative signing key. No user wallets, staked assets, locked assets, burned scores, Moat Points or audited smart contracts were impacted.
The impacted automated reward system was not yet fully migrated to the desired V3 multisig architecture, which allowed a legacy builder key with increased permissions to maintain control of reward wallets. Stolen funds were consolidated on Avalanche, bridged to Solana through Wormhole, and passed to a single Fireblocks-related wallet.
The compromised automated reward infrastructure has been fully shut down, compromised permissions have been removed for the admin key, and backend automated reward wallet system is being rebuilt with fresh wallets and an upgraded security architecture. We are actively coordinating with impacted communities and are working toward the best path forward to help restore affected Moats.
Please see the full details of the incident, along with our response below.
Overview
The Moats App team detected unauthorized activity affecting automated reward wallets on Avalanche following the compromise of a backend signing authority used in reward infrastructure.
The affected system was part of the automated reward wallet infrastructure slated to be migrated into a multisig controlled administrative setup under the V3 architecture upgrade. This migration never fully took place though and a backend signing key, known internally as the builder key, was still able to sign transactions across automated reward wallets.
This signing power was generated by a former developer wallet that was used in the initial V1 and V2 infrastructure before the migration to multisig-based management. It maintained escalated permissions over automated reward wallet operations and may have been compromised during its lifespan. The precise compromise vector is still under study.
Using this signing authority, unauthorized transactions were executed across multiple automated reward wallets on Avalanche. Funds were consolidated into intermediary wallets under attacker control prior to cross chain movement. The activity observed reflects structured abuse of residual administrative permissions rather than any exploit of audited smart contracts or protocol level systems.
Following detection, all automated reward systems were paused, compromised signing permissions were revoked, and investigation was initiated across Avalanche and Solana ecosystems. Coordination with affected ecosystem participants is ongoing, with recovery efforts actively in progress.
This incident was strictly limited to backend automated reward wallet infrastructure on Avalanche. No user wallets were affected, no Moat points or Map scores were altered, and no staked, locked, or burned assets were impacted. The audited smart contract system remained fully secure, with no protocol level vulnerabilities identified.
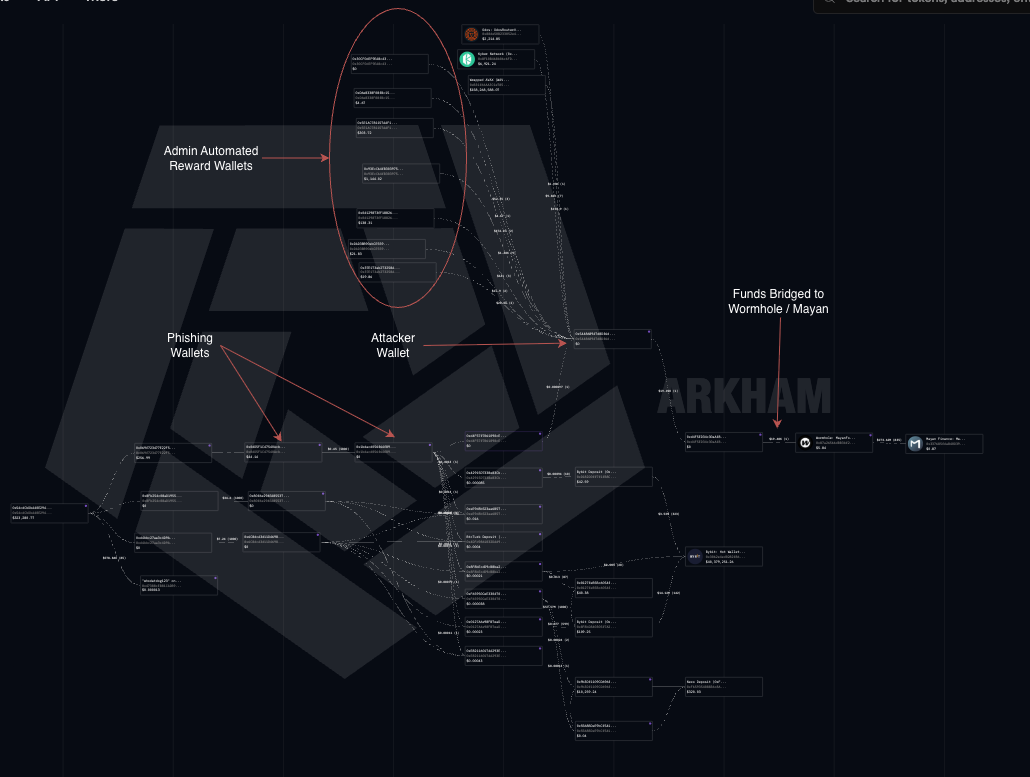
End-to-End Fund Flow: Consolidation, Bridging, and Post-Bridge Movement
The initial movement of funds occurred entirely on Avalanche. Multiple automated reward wallets were drained and consolidated into intermediary wallets using a compromised legacy builder key. These wallets were part of the reward system and had not yet been migrated to multisig under the V3 upgrade. Once access was obtained through the legacy signing authority, funds were consolidated into a single control wallet on Avalanche.
The attack began on Avalanche at approximately 2:00 AM EST / 6:00 AM UTC and completed within a few minutes. The attacker used address 0x544868947d8Df6d976dB024d59Dec0a0B5eF59f8 to execute a systematic attack on the automated reward wallet system.
All active Moats reward wallets were targeted in descending order of value. Wheremalek was hit first as the largest wallet followed by Gator, Papi, TOPIA, PhotoBooth, Funk, Lil Coq, and other automated reward wallets in the system. Each wallet was also drained of its remaining AVAX, which was deposited for gas related to depositing rewards.
All extracted assets were converted into AVAX and consolidated under the attacker address. Funds were then transferred from 0x544868947d8Df6d976dB024d59Dec0a0B5eF59f8 to intermediary wallet 0xd4F5ED34c30aAf83E0588D4ed8e67d6bDa5bB7de.
From there the full balance was sent to bridge routing address 0x87a26566dBB3bf206634C1792A96Ff4989E3F56E which corresponds to Wormhole / Mayan bridge infrastructure.
The full cross-chain routing flow can be viewed via Wormholescan.
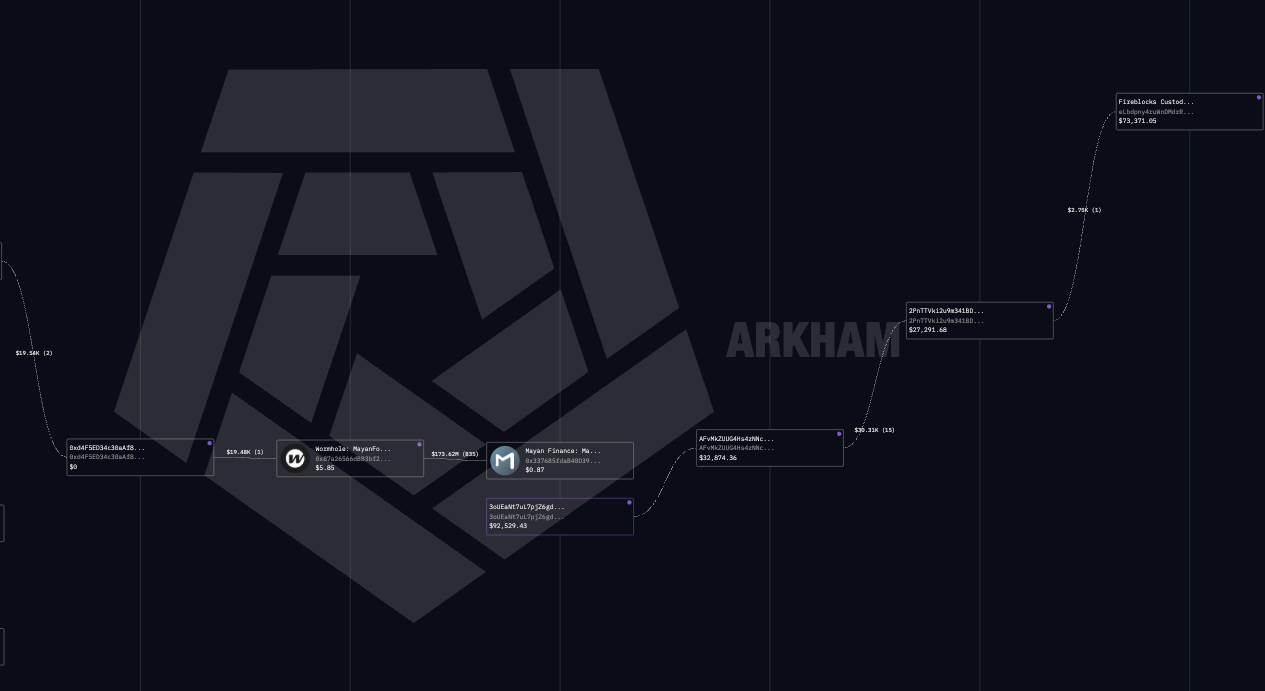
After settlement on Solana, funds were received at AFvMkZUUG4Hs4zNNcrEMerma6T8ZXX5ddBSh23dpdNhn. The funds first moved into 2PnTTVki2u9m341BDMJ3pybmJncZqk7GE2UZeXTU4Qk5 and were subsequently forwarded to eLbdpny4ruWkH8wEs35wuUTvbtKt5npemDBma6ezE.
Per Arkham Intelligence labeling, several wallets on Solana are associated with Fireblocks infrastructure clusters, including eLbdpny4ruWkH8wEs35wuUTvbtKt5npemDBma6ezE, which received the total stolen admin reward wallet funds. This cross chain flow of funds is mapped below.
You can review this entire tracing graph on Arkham with this link https://intel.arkm.com/tracer/7d776da7-56b7-49af-9e06-20b62fe2c843
We are currently requesting assistance from the community and our partners to help in getting in touch with Fireblocks, as this may provide additional context for understanding the custody-labeled routing patterns observed in the post-bridge flow and will us assist in working with law enforcement.
Impact Assessment and Ecosystem Exposure
The confirmed impact of this incident is limited to admin-controlled automated reward wallets tied to backend infrastructure on Avalanche. No user funds were impacted, no smart contract systems were compromised, and no staking, locked, or burned assets were affected. Core protocol systems remained secure throughout the incident, and no vulnerabilities were identified within audited contracts or protocol logic.
The affected infrastructure supported automated reward distribution across multiple Moats utilizing the legacy reward wallet system. As a result, several ecosystem projects experienced losses tied specifically to operational reward wallets connected to the compromised signing infrastructure.
Wheremalek experienced approximately 533 million tokens sold during the incident, representing an estimated value of roughly $5,580 at the time of attack. Over 90 million were rebought on the market by the Moats team directly following the attack for roughly $2,000.
PhotoBooth experienced approximately 180 million tokens sold, representing an estimated value of roughly $446. Arena tokens used as rewards were also lost in attack.
Gator experienced approximately 940 million tokens sold, representing an estimated value of roughly $1,391. The moats team also acquire 109 million GATOR at the time of the attack. This will be used to help being reimbursement for the Gator team.
Papi experienced approximately 1 billion tokens sold, representing an estimated value of roughly $2,400 at the time of the attack.
TOPIA was also impacted, including approximately 30 million BANDS tokens valued at roughly $640, approximately 165 million TOPIA valued at roughly $1,490, additional ~$210 worth of AVLO exposure, and other connected reward assets totaling close to $6,000 usd. Topia had over 28 different reward tokens in their system, thankfully not all had active balances at the time of the attack.
Funk lost several percentage points of total token supply.
Lil Coq experienced losses including approximately 18 WAVAX in rewards.
Additional Moats including Hefe, Bensi, and others utilizing this reward infrastructure also incurred losses across affected reward wallets during the incident window.
The total damages were ~19,000 usd worth of rewards, mostly in memecoins.
All avax held in the wallets for gas was taken in the attack. This equated roughly 7 avax worth of gas money. All will be reimbursed.
At this time, we are actively coordinating with impacted projects and community administrators to determine the most effective path forward for restoration and remediation efforts. Our goal remains to work toward making impacted communities whole where feasible while the broader investigation and infrastructure remediation process continues. We expect the total compensation for lost rewards to be roughly ~40% of funds. The Moats App is entirely self funded and this entire bailout is coming directly out of the teams pocket, as we do not have a moats app treasury and are fully self funded at this time. As a result, we unfortunately do not have any ability to cover full losses, and we apologize for this. Lost reward tokens, as described above, were bridged off to Solana and were not able to be recovered yet. We are still working to connect with Fireblocks to explore future recovery options for these stolen rewards.
We want to reiterate that the Moats App smart contracts, which facilitate staking, locking, and burning, were not impacted in this attack. All user funds are safe and unaffected by this incident.
Immediate Response and Moving Forward
All automated reward distribution systems have been paused and compromised backend signing permissions have been revoked. The reward automation system has been fully shut down, and coordination has begun with infrastructure partners to disable or suspend any associated tools, integrations, and services built on top of the affected reward infrastructure.
The legacy signing authority associated with the builder key has been removed from backend systems. We are also attempting to engage Fireblocks to determine whether any additional visibility or assistance can be provided in identifying the final recipients of the bridged funds, based on the wallet clusters and infrastructure labels observed in the post bridge activity.
As part of remediation, the existing backend reward infrastructure will not be restarted in its prior form. A fresh set of reward wallets and a fully rebuilt backend database architecture will be deployed. We are also evaluating additional security upgrades, including creator confirmed withdrawal flows and optional two factor authentication for automated reward execution.
We will also be introducing updated operational guidance for reward administrators once the system is restored. Specifically, we will be requesting that reward programs avoid preloading more than one to two months of emissions into automated reward wallets. While the infrastructure itself is being rebuilt with improved security controls and the legacy builder key has been fully removed, limiting long duration funding exposure reduces systemic risk. Long horizon reward streaming creates unnecessary target value accumulation in operational wallets, and we strongly recommend using multisig custody for longer term reward reserves with periodic deposits into the automated system rather than large upfront allocations.
The investigation remains active and is focused on understanding how the legacy signing authority remained active within the reward system despite the intended migration to multisig governance. Additional work is underway to reconstruct historical signer exposure across reward infrastructure and validate internal access boundaries during the V3 transition.
This incident was isolated to backend operational reward infrastructure and did not impact the Moats smart contract system or any user controlled assets. The vulnerability was contained to an unaudited administrative automation layer, which has now been fully disabled and replaced. We take full responsibility for this failure in operational controls and are actively working with impacted communities to coordinate recovery and reimbursement pathways where possible.
Moats is an entirely self-funded project run by a very small team. The application is operated by just three people, with development and infrastructure fully funded out of pocket by myself. We do not currently have a treasury, outside funding, or institutional backing. Because of this, our resources are limited compared to larger teams and protocols. Even so, I will personally be covering a portion of the losses out of pocket at ~40% of total value lost, while we continue coordinating recovery efforts with stakeholders and affected communities.
In addition to the ongoing buyback program, we will be using our platform’s early user airdrop boost mechanisms to provide additional weight towards the MAPS system for the most heavily impacted Moats and communities as part of longer term remediation efforts. We recognize this is not a perfect fix. We are committed to supporting our affected communities long term and helping recover stolen funds the best of our ability.
We are also working with law enforcement and attempting to engage Fireblocks and other ecosystem participants in an effort to trace and potentially recover the stolen assets. We understand recovery is never guaranteed in situations like this, but we are committed to pursuing every realistic avenue available.
We are actively requesting help getting in touch with Fireblocks. Please reach out to me (@minerxbt on Telegram/@minerminer on X) or hop in our Moats App discord if you are able to connect us with their team.
I want to give a special shoutout to the individuals who assisted during the investigation of this attack and helped while this incident was actively unfolding. Thank you to Passivejunky, Rabisright, Matthew Malek, and all of the admins that provided information to my team. Your support and assistance during this incident was beyond incredible and I truly appreciate the help.
We remain committed to full transparency throughout this investigation and will continue publishing updates as additional onchain data becomes available. All information referenced in this report is public and verifiable onchain, and we encourage independent review and analysis from the community. If anyone identifies additional relevant transactions, patterns, or wallet connections, we welcome those findings and are actively reviewing community submitted leads. Please bring these findings to our Discord, post them on the timeline and tag us, or DM us directly on X.
Finally, I want to thank every user, admin, and partner team for their patience and support throughout this incident. We understand the impact this has had and we do not take that lightly. I want to express my sincerest apologies that this incident occurred in the first place. We are fully committed to making this situation right and will continue coordinating closely with affected teams over the coming days and weeks as recovery and remediation efforts progress.
Onward and upwards.
From,
Alex Miner